DarkSide was responsible for Colonial Pipeline ransomware attack, promises to pick targets more carefully in the future
A hot potato: The v,500-mile Colonial Pipeline has been offline for the last four days, later on a ransomware attack compromised its estimator network. DarkSide, an Eastern European group of cybercriminals believed to be the authors of the attack, posted a statement on the nighttime web noting that its sole goal is money, with no connectedness to geopolitical interests and no intention of "creating problems for society."
Recently, the primary fuel supply line serving the US E Coast was shut down later on its operator suffered a security breach in its digital infrastructure. The Colonial Pipeline stretches for over 5,500 miles to provide around 45 percent of the fuel needs of the region, which makes this potentially the largest successful cyberattack on U.s. infrastructure to date.
The company says it close down the main office of the pipeline as a precaution, while information technology only brought "smaller lateral lines between terminals and delivery points" dorsum upwardly. A third party security firm was hired to investigate the incident, and preliminary findings point out to ransomware attack that affected Colonial's business estimator systems. The attackers accept encrypted almost 100 gigabytes of data from the Georgia-based visitor and are threatening to release it to the public if it doesn't pay the bribe.
Today, the FBI confirmed suspicions that a grouping of Eastern European cybercriminals calling itself DarkSide is behind the assail, noting "nosotros proceed to work with the company and our government partners on the investigation." At the same time, the hacker group posted a statement on the night web explaining that its 1 and only goal is to make coin, and that it's not tied to a "defined" government or political entity.

Interestingly, the grouping as well explained that it has no intention of "creating issues for lodge," which is an understatement of the ruckus created through the disruption of almost one-half the supply of gasoline and diesel to the United states of america Eastward Declension.
And while it wouldn't say how much information technology demanded in ransom money from Colonial, it did merits that it has breached more than 80 companies since August 2022, subsequently previously extracting millions from individuals.
The most peculiar office of DarkSide's statement is where the group promises to innovate a moderation process into its workflow in order to "avoid social consequences in the futurity."
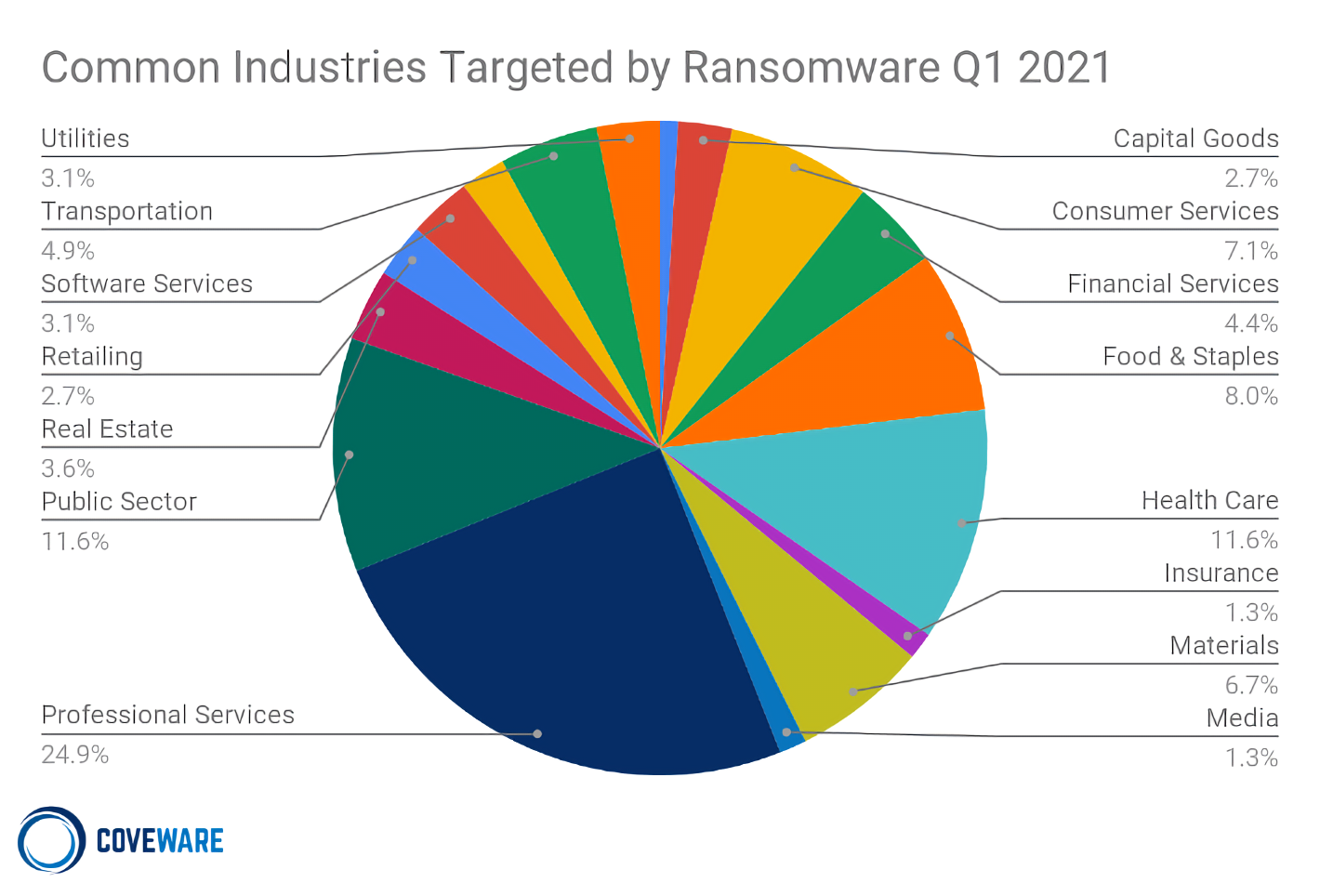
Boston-based security firm Cybereason told CNBC that DarkSide is a "ransomware as a service" provider that tries to project the paradigm of being ethical, with clear rules of conduct that are against attacking medical and educational institutions, government agencies, and even not-profit organizations -- specially if they're located in former fellow member countries of the Soviet bloc. The group fifty-fifty claims to donate portion of its profits to clemency.
Colonial doesn't say if it will pay the ransom, but the company is optimistic about its goal to "substantially restore operational service past the finish of the week." The Biden administration has issued an emergency announcement in 17 states and Washington DC in an effort to keep deliveries going and help Colonial return to normal operations equally soon as possible.
In other news, Axa SA, one of the biggest insurance companies in Europe, announced that it will stop offer policies that comprehend ransomware payments in French republic, which could encourage more insurance companies to follow suit.
This probably shouldn't surprise anyone, considering the recent surge in ransomware attacks on companies big and small, including figurer manufacturer Acer and game publisher CD Projekt Crimson. Information technology's estimated that in 2022, over 41 percent of cyber insurance claims came from ransomware, with damages totaling more than $20 billion, almost double the corporeality estimated for 2022.
The number of ransomware attacks has increased by an club of magnitude in the concluding twelve months, but at least there'southward been a decrease in ransomware payments as more victims refuse to pay. Today'southward news is, perhaps, the best reminder to always create multiple backups of your of import files and exercise maximum circumspection when receiving suspicious emails or invitation links on messaging platforms.
Source: https://www.techspot.com/news/89615-darkside-responsible-colonial-pipeline-ransomware-attack-promises-pick.html
Posted by: lyonrild1968.blogspot.com


0 Response to "DarkSide was responsible for Colonial Pipeline ransomware attack, promises to pick targets more carefully in the future"
Post a Comment